Plesk is a paid server management interface. Its source code is encrypted so as not to be adaptable, except when running within a plesk environment. Initially created in novosibirsk, USA, plesk was launched in 2001. In 2003, the project was acquired by swsoft ( en ), which became parallels, inc.
in 2008. In December 2015, plesk became a fully owned entity, which has since been acquired by oakley capital. Its ease of use and its ability to allow a non-expert user to manage the server makes it a well-known tool in the field of dedicated server administration.
Discover Plesk’s website and blog
The Plesk website https://www.plesk.com/
The plesk Blog https://www.plesk.com/blog/
Some information about Plesk
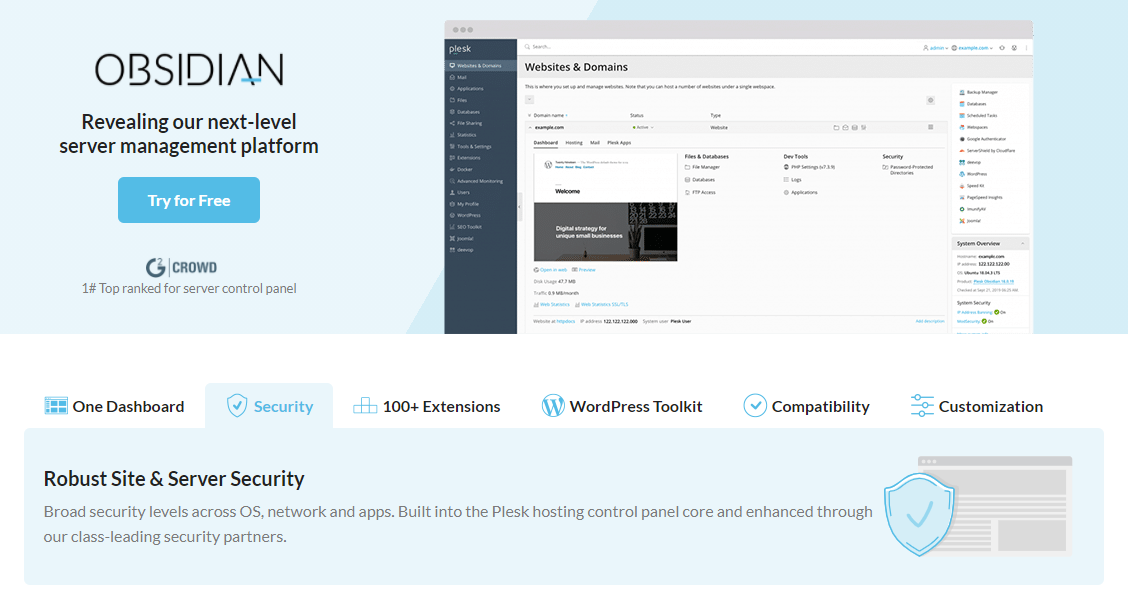
Plesk handles the commissioning of new websites, advanced access rights to the administration interface, email management, and dns. Plesk web administration made easy and secure with plesk plesk is the market leading multi-platform control panel. It is a simple and convenient way to administer your web services.
Through the browser-based plesk interface, you can instantly create e-mail accounts, configure your domain features, manage your web files, install an application, create a database, manage your ftp access, and more. Plesk simplifies these tasks so that you can accomplish them without the need to be disciplined with server commands and shell scripts.
New editions of plesk should create targeted solutions for the following profiles: web administrators, web professionals and hosting resellers. Each edition simplifies key web management activities. All editions include integrated server-to-site security, resulting in a more reliable infrastructure and reduced support costs.
View plesk news on the social networks
So… why would one use a control panel to manage hosting? Here´s a whole list of reasons 👇 https://t.co/RTXaTuSGYC
— Plesk (@Plesk) February 25, 2021
WordPress toolkit
WordPress toolkit with plesk security and mass management tools for wordpress hosting centrally manage multiple wordpress installations as well as plug-ins, themes and updates. easy installation and removal of wordpress as well as plug-ins and themes.
Secure new wordpress installations and enhance the security of existing installations by applying the most commonly recommended security features with healing support.